
Hello and welcome! Today, we’re diving into the world of NoVNC-based advanced phishing attacks. Ever heard of it? NoVNC is a tool that lets you control someone else’s computer screen straight from your web browser. Originally, it was all about tech support and remote server management. But now, hackers have gotten crafty, using it for advanced phishing methods.
Phishing? Yeah, that’s when someone tricks you into handing over your private info, like passwords or credit card numbers. And guess what? They’re pulling it off with NoVNC in some pretty sneaky ways.
In this tutorial, we’ll walk you through everything, from how NoVNC works to how hackers hide their tricks in it. By the end, you’ll have a clear picture of how these attacks go down and how to keep yourself safe. Ready to dive in?
Table of Contents
What is NoVNC?
NoVNC, short for Network Virtual Terminal Protocol over VNC, is a tool that lets you control another computer’s desktop right from your web browser. Let’s study it in detail.
First off, we have VNC, which stands for Virtual Network Computing. With VNC, you’ve got two main parts: the “server” on the remote machine and the “viewer” on your local machine. The server grabs whatever’s on the remote screen and sends it to your viewer, while the viewer sends your commands back to the server, letting you control that remote machine like you’re right there.
Now, here’s where NoVNC comes in. It takes that same idea and makes it even cooler by letting you access VNC sessions straight from your web browser. No need to install any extra software. Just fire up your browser, type in the right web address, and boom! You’re peering into another computer’s world.
JavaScript, HTML5 canvas, and WebSockets come together to create a virtual VNC client right in your browser, giving you the power to connect to VNC servers from anywhere with an internet connection.
Plus, NoVNC has got your back when it comes to security. It supports various authentication methods, so you can rest easy knowing your remote desktop sessions are safe and sound.
In a nutshell, NoVNC is like having a remote control for any computer, all packed neatly into your web browser. Pretty neat, huh?
How to create a Phishing link using NoVNC?
In this detailed tutorial, we’ll guide you through the step-by-step process of executing advanced phishing attacks using NoVNC (Network Virtual Terminal Protocol over VNC). Follow along carefully to understand how hackers leverage this tool to gain unauthorized access to sensitive information.
Step 1: Setting Up a Cloud VPS
Choose a reliable Cloud Virtual Private Server (VPS) provider such as AWS, Digital Ocean, or any reputable service that offers cloud hosting options.
So, I’ve got this Kali Linux 2023 VPS fired up, and we’re about to kick off the setup for NoVNC inside it. The first thing is to get that Chromium browser installed on your Kali system.
Step 2: Embedding Phishing Page within NoVNC
Clone the NoVNC repository from its official GitHub page onto your Cloud VPS using the command:
git clone https://github.com/novnc/noVNC.gitWithin the NoVNC interface, integrate your phishing page discreetly. Utilize HTML and CSS techniques to blend the advanced phishing content seamlessly into the NoVNC environment, making it appear authentic and unsuspecting to victims.
Step 3: Initiating NoVNC Server
Start the NoVNC server on your Cloud VPS by executing the following command:
./noVNC/utils/novnc_proxy --vnc 0.0.0.0:5901 --listen 80This command configures the NoVNC server to listen for incoming connections on ports 5901 and 80, facilitating access to the phishing pages via standard web browsers.
Step 4: Accessing Computer Screen via Browser
Open a new terminal window on your Cloud VPS and initiate the Chromium browser in kiosk mode with the command:
chromium --no-sandbox --app=https://gmail.com --kioskThis command launches the Chromium browser and open gmail.com in full-screen mode, overlaying it onto the NoVNC session, providing a seamless user experience for interacting with the phishing pages. You can use any website like Facebook or Instagram in place of Gmail.
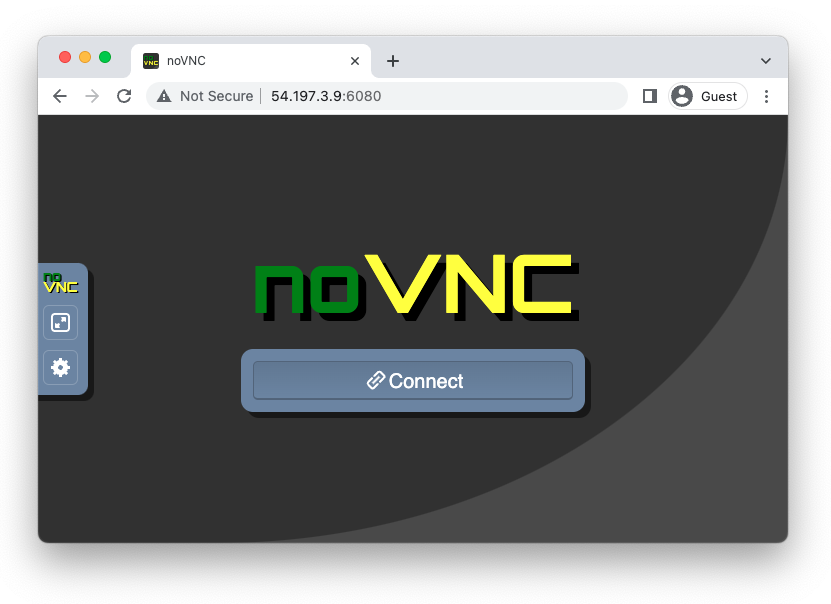
Step 5: Your Phishing Link is created
Alright, now your computer or VPS is accessible through any browser. Just use this URL to open it up in your browser:
http://YourIP/vnc.html?autoconnect=true&password=VNCPASSOnce you do that, you’ll see gmail.com pop up right in front of you, just like we typed it into the terminal session.
Step 6: Implementing Advanced Phishing URL Evasion
Employ advanced evasion techniques such as URL obfuscation, encryption, and proxy servers to ensure that the phishing URLs remain undetected by security measures and browser filters. Don’t worry, you can also use the above URL as it is.
Step 7: Capturing and Exploiting Credentials
Encourage victims to interact with the phishing pages embedded within the NoVNC session. Prompt them to enter sensitive information such as usernames, passwords, and other confidential data.
So, when someone logs in through this open window, all those login credentials are actually hitting your VPS machine where you fired up the server. It’s like you’re interacting with the original website directly, not some advanced phishing scam. But, because it’s accessed through NoVNC, all your info gets saved on the hacker’s VPS. Just remember, everything you type in this browser is running on a full operating system behind the scenes.
Conclusion
Congratulations on completing this tutorial on advanced phishing with NoVNC! You’ve now got some serious insights into how hackers use this powerful tool to fool people and swipe their sensitive info.
It’s super important to keep your guard up and stay in the know about cybersecurity threats to keep yourself and your data safe.
Remember, these advanced phishing attacks can hit anyone, so always be careful online and never spill the beans on personal stuff unless you’re 110% sure about who you’re dealing with. And hey, make sure your software and security setups are all up to date too.
By getting wise to the tricks of the trade and following top-notch cybersecurity tips, you can lock down your online identity and dodge those advanced phishing scams like a pro.
The concept is inspired from @mr.d0x
FAQs
- What is the difference between VNC and NoVNC?
VNC (Virtual Network Computing) is your classic desktop-sharing setup where you need to install client software on your local machine. On the other side, NoVNC (Network Virtual Terminal Protocol over VNC) is a web-based version of VNC. With NoVNC, you can hop into remote desktop sessions straight from your web browser, with no extra software needed. - How do I install NoVNC?
To install NoVNC, you’ll need to grab the NoVNC repository from its official GitHub page and set it up on a server. Just follow the instructions laid out in the repository’s documentation to get NoVNC up and running on whatever platform you prefer. - How can NoVNC be used for phishing attacks?
Hackers can embed phishing pages within the NoVNC interface and trick unsuspecting users into entering their credentials. By presenting convincing phishing pages within the NoVNC session, hackers can capture sensitive information such as usernames, passwords, and other personal data. - How to connect with NoVNC?
To connect with NoVNC, users need to access the NoVNC session via a web browser. They can do so by entering the URL provided by the NoVNC server administrator, along with any necessary authentication credentials, to establish a connection and access the remote desktop session. - What is the use of NoVNC?
NoVNC is commonly used for remote desktop access and server administration. It allows users to control remote desktop environments directly through a web browser, making it convenient for accessing systems from anywhere with an internet connection. - What is advanced phishing?
Advanced phishing refers to sophisticated phishing techniques used by cybercriminals to deceive users and steal sensitive information. This may involve the creation of convincing phishing pages, social engineering tactics, and exploitation of vulnerabilities in software and systems. Using NoVNC for phishing attacks is an example of advanced phishing, as it leverages web-based technology to facilitate unauthorized access to sensitive data.
Wiretap System Breach Exposes Risks of Government-Installed Backdoors in U.S. Telecoms [2024]
Introduction In recent news, the wiretap system breach by China-backed hackers has raised significant alarm…
Password Cracking with Hydra: Step-by-Step Ethical Hacking Guide [Part 11 of Ethical Hacking Series]
Introduction to Password Cracking Password cracking is a method used in cybersecurity to recover passwords…
Step-by-Step Guide to Crack WiFi Passwords with Aircrack-ng [Part 10 of Ethical Hacking Series]
Introduction to Wireless Network Haking Welcome to Part 10 of our Ethical Hacking series, where…
Web Attacks: 7 Tools for OWASP Top 10 Testing [Part 9 of Ethical Hacking Series]
Introduction Welcome to Part 9 of our Ethical Hacking series, where we dive into the…
Post-Exploitation Mastery: Maintaining Access Techniques Explained [Part 8 of Ethical Hacking Series]
Introduction Welcome to Part 8 of our Ethical Hacking series: Post-Exploitation Techniques: Maintaining Access. In…
Stay Safe from Rising Quishing Attack EV at Charging Stations
Electric vehicle (EV) owners need to be cautious as a new cyber threat known as…



![Step-by-Step Guide to Crack WiFi Passwords with Aircrack-ng (Wireless Password Hacking) [Part 10 of Ethical hacking series]](https://hackproofhacks.com/wp-content/uploads/2024/09/Grey-Minimalist-Tips-Blog-Banner-8-1024x576.png)
![Web Attacks: 7 Tools for OWASP Top 10 Testing [part 9 of Ethical Hacking Series]](https://hackproofhacks.com/wp-content/uploads/2024/09/Grey-Minimalist-Tips-Blog-Banner-7-1024x576.png)





